Abstract
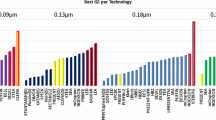
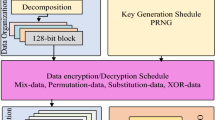
The main purpose of block ciphers is to ensure data confidentiality, integrity and robustness against security attacks. Nevertheless, several ciphers also try to be efficient in encryption and decryption phases, have a small energy consumption and/or small memory footprint. These ciphers are usually optimized for certain software or hardware platforms. In this work, we analyze lightweight and classic block ciphers. Further, we implement an application which employs 20 current software-oriented block ciphers and benchmark them on a smartphone. The experimental results and the performance evaluation of ciphers are presented. Moreover, we compare the performance of two forms of implementation by native JAVA cryptography APIs and by an external cryptography provider. In addition, we measure the current consumption of the selected block ciphers on a smartphone.
Access this chapter
Tax calculation will be finalised at checkout
Purchases are for personal use only
Similar content being viewed by others
References
Rinne, S., Eisenbarth, T., Paar, C.: Performance analysis of contemporary light-weight block ciphers on 8-bit microcontrollers. In: ECRYPT Workshop SPEED-Software Performance Enhancement for Encryption and Decryption booklet, Citeseer, pp. 33–43 (2007)
Eisenbarth, T., Kumar, S.: A survey of lightweight-cryptography implementations. Des. Test Comput., IEEE 24(6), 522–533 (2007)
Çakiroglu, M.: Software implementation and performance comparison of popular block ciphers on 8-bit low-cost microcontroller. Int. J. Phys. Sci. 5(9), 1338–1343 (2010)
Eisenbarth, T., et al.: Compact implementation and performance evaluation of block ciphers in ATtiny devices. In: Mitrokotsa, A., Vaudenay, S. (eds.) AFRICACRYPT 2012. LNCS, vol. 7374, pp. 172–187. Springer, Heidelberg (2012)
Wu, W., Zhang, L.: LBlock: a lightweight block cipher. In: Lopez, J., Tsudik, G. (eds.) ACNS 2011. LNCS, vol. 6715, pp. 327–344. Springer, Heidelberg (2011)
Kerckhof, S., Durvaux, F., Hocquet, C., Bol, D., Standaert, F.-X.: Towards green cryptography: a comparison of lightweight ciphers from the energy viewpoint. In: Prouff, E., Schaumont, P. (eds.) CHES 2012. LNCS, vol. 7428, pp. 390–407. Springer, Heidelberg (2012)
Weis, R., Lucks, S.: The performance of modern block ciphers in JAVA. In: Schneier, B., Quisquater, J.-J. (eds.) CARDIS 1998. LNCS, vol. 1820, pp. 125–133. Springer, Heidelberg (2000)
Paik, J.H., Seo, S.C., Kim, Y., Lee, H.J., Jung, H.C., Lee, D.H.: An efficient implementation of block cipher in android platform. In: 2011 5th FTRA International Conference on Multimedia and Ubiquitous Engineering (MUE), pp. 173–176. IEEE (2011)
Lewerentz, A., Lindvall, J., Fogelström, N.D.: Performance and energy optimization for the android platform (2012)
Bogdanov, A., Khovratovich, D., Rechberger, C.: Biclique cryptanalysis of the full AES. In: Lee, D.H., Wang, X. (eds.) ASIACRYPT 2011. LNCS, vol. 7073, pp. 344–371. Springer, Heidelberg (2011)
Kara, O., Manap, C.: A new class of weak keys for blowfish. In: Biryukov, A. (ed.) FSE 2007. LNCS, vol. 4593, pp. 167–180. Springer, Heidelberg (2007)
Lu, J., Wei, Y., Kim, J., Pasalic, E.: The higher-order meet-in-the-middle attack and its application to the camellia block cipher. In: Part at the First Asian Workshop on Symmetric Key Cryptography (ASK 2011), August 2011. https://sites.google.com/site/jiqiang.
Moriai, S., Shimoyama, T., Kaneko, T.: Higher order differential attack of a CAST cipher. In: Vaudenay, S. (ed.) FSE 1998. LNCS, vol. 1372, pp. 17–31. Springer, Heidelberg (1998)
Pestunov, A.: Differential cryptanalysis of 24-round cast-256. In: IEEE Region 8 International Conference on Computational Technologies in Electrical and Electronics Engineering, SIBIRCON 2008, pp. 46–49. IEEE (2008)
Tezcan, C.: The improbable differential attack: cryptanalysis of reduced round CLEFIA. In: Gong, G., Gupta, K.C. (eds.) INDOCRYPT 2010. LNCS, vol. 6498, pp. 197–209. Springer, Heidelberg (2010)
Junod, P.: On the complexity of matsui’s attack. In: Vaudenay, S., Youssef, A.M. (eds.) SAC 2001. LNCS, vol. 2259, pp. 199–211. Springer, Heidelberg (2001)
Phan, R.-W.: Related-Key attacks on triple-DES and DESX variants. In: Okamoto, T. (ed.) CT-RSA 2004. LNCS, vol. 2964, pp. 15–24. Springer, Heidelberg (2004)
Biryukov, A., Wagner, D.: Advanced slide attacks. In: Preneel, B. (ed.) EUROCRYPT 2000. LNCS, vol. 1807, pp. 589–606. Springer, Heidelberg (2000)
Dinur, I., Dunkelman, O., Shamir, A.: Improved attacks on full GOST. In: Canteaut, A. (ed.) FSE 2012. LNCS, vol. 7549, pp. 9–28. Springer, Heidelberg (2012)
Hong, D., Koo, B., Kwon, D.: Biclique attack on the full HIGHT. In: Kim, H. (ed.) ICISC 2011. LNCS, vol. 7259, pp. 365–374. Springer, Heidelberg (2012)
Khovratovich, D., Leurent, G., Rechberger, C.: Narrow-bicliques: cryptanalysis of full IDEA. In: Pointcheval, D., Johansson, T. (eds.) EUROCRYPT 2012. LNCS, vol. 7237, pp. 392–410. Springer, Heidelberg (2012)
Dunkelman, O., Keller, N., Shamir, A.: A practical-time related-key attack on the KASUMI cryptosystem used in GSM and 3G telephony. In: Rabin, T. (ed.) CRYPTO 2010. LNCS, vol. 6223, pp. 393–410. Springer, Heidelberg (2010)
Wei, L., Rechberger, C., Guo, J., Wu, H., Wang, H., Ling, S.: Improved meet-in-the-middle cryptanalysis of KTANTAN (Poster). In: Parampalli, U., Hawkes, P. (eds.) ACISP 2011. LNCS, vol. 6812, pp. 433–438. Springer, Heidelberg (2011)
Yu, X., Wu, W., Li, Y., Zhang, L.: Cryptanalysis of reduced-round KLEIN block cipher. In: Wu, C.-K., Yung, M., Lin, D. (eds.) Inscrypt 2011. LNCS, vol. 7537, pp. 237–250. Springer, Heidelberg (2012)
Park, J.: Security analysis of mcrypton proper to low-cost ubiquitous computing devices and applications. Int. J. Commun. Syst. 22(8), 959–969 (2009)
Abdul-Latip, S.F., Reyhanitabar, M.R., Susilo, W., Seberry, J.: On the security of NOEKEON against side channel cube attacks. In: Kwak, J., Deng, R.H., Won, Y., Wang, G. (eds.) ISPEC 2010. LNCS, vol. 6047, pp. 45–55. Springer, Heidelberg (2010)
Abed, F., Forler, C., List, E., Lucks, S., Wenzel, J.: Biclique cryptanalysis of the present and led lightweight ciphers. Technical report, Cryptology ePrint Archive, Report 2012/591 (2012)
Kelsey, J., Schneier, B., Wagner, D.: Related-key cryptanalysis of 3-WAY, Biham-DES, CAST, DES-X, NewDES, RC2, and TEA. In: Han, Y., Quing, S. (eds.) ICICS 1997. LNCS, vol. 1334, pp. 233–246. Springer, Heidelberg (1997)
Kaliski, B., Yin, Y.: On the security of the rc5 encryption algorithm. Technical report, RSA Laboratories Technical Report TR-602. To appear (1998)
Shimoyama, T., Takenaka, M., Koshiba, T.: Multiple linear cryptanalysis of a reduced round RC6. In: Daemen, J., Rijmen, V. (eds.) FSE 2002. LNCS, vol. 2365, p. 76. Springer, Heidelberg (2002)
Galice, S., Minier, M.: Improving integral attacks against rijndael-256 Up to 9 rounds. In: Vaudenay, S. (ed.) AFRICACRYPT 2008. LNCS, vol. 5023, pp. 1–15. Springer, Heidelberg (2008)
Sung, J.: Differential cryptanalysis of eight-round seed. Inf. Process. Lett. 111(10), 474–478 (2011)
Nguyen, P.H., Wu, H., Wang, H.: Improving the algorithm 2 in multidimensional linear cryptanalysis. In: Parampalli, U., Hawkes, P. (eds.) ACISP 2011. LNCS, vol. 6812, pp. 61–74. Springer, Heidelberg (2011)
Chung-Wei Phan, R.: Cryptanalysis of full skipjack block cipher. Electron. Lett. 38(2), 69–71 (2002)
Lucks, S.: The saturation attack - A bait for twofish. In: Matsui, M. (ed.) FSE 2001. LNCS, vol. 2355, pp. 1–15. Springer, Heidelberg (2002)
Sasaki, Y., Wang, L., Sakai, Y., Sakiyama, K., Ohta, K.: Three-subset meet-in-the-middle attack on reduced XTEA. In: Mitrokotsa, A., Vaudenay, S. (eds.) AFRICACRYPT 2012. LNCS, vol. 7374, pp. 138–154. Springer, Heidelberg (2012)
Daemen, J., Rijmen, V.: The Design of Rijndael: AES-the Advanced Encryption Standard. Springer, Heidelberg (2002)
Schneier, B.: Description of a new variable-length key, 64-bit block cipher (Blowfish). In: Anderson, R. (ed.) FSE 1993. LNCS, vol. 809, pp. 191–204. Springer, Heidelberg (1994)
Aoki, K., Ichikawa, T., Kanda, M., Matsui, M., Moriai, S., Nakajima, J., Tokita, T.: Specification of camellia-a 128-bit block cipher (2000)
Adams, C.: The cast-128 encryption algorithm (1997)
Gilchrist, J., Adams, C.: The cast-256 encryption algorithm (1999)
Shirai, T., Shibutani, K., Akishita, T., Moriai, S., Iwata, T.: The 128-Bit blockcipher CLEFIA (extended abstract). In: Biryukov, A. (ed.) FSE 2007. LNCS, vol. 4593, pp. 181–195. Springer, Heidelberg (2007)
Smid, M., Branstad, D.: Data encryption standard: past and future. Proc. IEEE 76(5), 550–559 (1988)
Leander, G., Paar, C., Poschmann, A., Schramm, K.: New lightweight DES variants. In: Biryukov, A. (ed.) FSE 2007. LNCS, vol. 4593, pp. 196–210. Springer, Heidelberg (2007)
Courtois, N.: Security evaluation of gost 28147–89 in view of international standardisation. Cryptologia 36(1), 2–13 (2012)
Hong, D., et al.: HIGHT: a new block cipher suitable for low-resource device. In: Goubin, L., Matsui, M. (eds.) CHES 2006. LNCS, vol. 4249, pp. 46–59. Springer, Heidelberg (2006)
Lai, X., Massey, J.L.: A proposal for a new block encryption standard. In: Damgård, I.B. (ed.) EUROCRYPT 1990. LNCS, vol. 473, pp. 389–404. Springer, Heidelberg (1991)
Specification of the 3gpp confidentiality and integrity algorithms, document 2: Kasumi specification (release 10) (2011)
Cannire, C., Dunkelman, O., Kneevi, M.: Katan and ktantan a family of small and efficient hardware-oriented block ciphers. In: Clavier, C., Gaj, K. (eds.) CHES 2009. LNCS, vol. 5747, pp. 272–288. Springer, Heidelberg (2009)
Gong, Z., Nikova, S., Law, Y.W.: KLEIN: a new family of lightweight block ciphers. In: Juels, A., Paar, C. (eds.) RFIDSec 2011. LNCS, vol. 7055, pp. 1–18. Springer, Heidelberg (2012)
Lim, C.H., Korkishko, T.: mCrypton - a lightweight block cipher for security of low-cost RFID tags and sensors. In: Song, J.-S., Kwon, T., Yung, M. (eds.) WISA 2005. LNCS, vol. 3786, pp. 243–258. Springer, Heidelberg (2006)
Daemen, J., Peeters, M., Van Assche, G., Rijmen, V.: Nessie proposal: Noekeon. In: First Open NESSIE Workshop (2000)
Bogdanov, A., Knudsen, L., Leander, G., Paar, C., Poschmann, A., Robshaw, M., Seurin, Y., Vikkelsoe, C.: Present: an ultra-light weight block cipher. In: Paillier, P., Verbauwhede, I. (eds.) CHES 2007. LNCS, vol. 4727, pp. 450–466. Springer, Heidelberg (2007)
Knudsen, L.R., Rijmen, V., Rivest, R.L., Robshaw, M.: On the design and security of RC2. In: Vaudenay, S. (ed.) FSE 1998. LNCS, vol. 1372, pp. 206–221. Springer, Heidelberg (1998)
Rivest, R.: The rc5 encryption algorithm. In: Preneel, B. (ed.) FSE 1994. LNCS, vol. 1008, pp. 86–96. Springer, Heidelberg (1995)
Contini, S., Rivest, R., Robshaw, M., Yin, Y.: The security of the rc6 tm block cipher. v1. 0. http://www.rsa.com/rsalabs/aes/security.pdf (1998)
Standaert, F.-X., Piret, G., Gershenfeld, N., Quisquater, J.-J.: SEA: a scalable encryption algorithm for small embedded applications. In: Domingo-Ferrer, J., Posegga, J., Schreckling, D. (eds.) CARDIS 2006. LNCS, vol. 3928, pp. 222–236. Springer, Heidelberg (2006)
Lee, J., Park, J., Lee, S., Kim, J.: The seed encryption algorithm. SEED (2005)
Anderson, R., Biham, E., Knudsen, L.: Serpent: A proposal for the advanced encryption standard. NIST AES Proposal (1998)
Biham, E., Biryukov, A., Shamir, A.: Cryptanalysis of skipjack reduced to 31 rounds using impossible differentials. In: Stern, J. (ed.) EUROCRYPT 1999. LNCS, vol. 1592, pp. 12–13. Springer, Heidelberg (1999)
Wheeler, D.J., Needham, R.M.: TEA, a tiny encryption algorithm. In: Preneel, B. (ed.) Fast Software Encryption. LNCS, vol. 1008, pp. 363–366. Springer, Heidelberg (1995)
Schneier, B., Kelsey, J., Whiting, D., Wagner, D., Hall, C., Ferguson, N.: Twofish: a 128-bit block cipher. NIST AES Proposal 15 (1998)
Ko, Y., Hong, S.H., Lee, W.I., Lee, S.-J., Kang, J.-S.: Related key differential attacks on 27 rounds of XTEA and full-round GOST. In: Roy, B., Meier, W. (eds.) FSE 2004. LNCS, vol. 3017, pp. 299–316. Springer, Heidelberg (2004)
Malina, L., Hajny, J.: Privacy-preserving framework for geosocial applications. Secur. Commun. Netw. 2013(8), 1–16 (2013)
Martinasek, Z., Zeman, V.: Innovative method of the power analysis. Radioengineering 22(2), 587 (2013)
Acknowledgments
This research work is funded by project SIX CZ.1.05/2.1.00/03.0072; the Technology Agency of the Czech Republic projects TA02011260 and TA03010818; the Ministry of Industry and Trade of the Czech Republic project FR-TI4/647.
Author information
Authors and Affiliations
Corresponding author
Editor information
Editors and Affiliations
Rights and permissions
Copyright information
© 2014 Springer International Publishing Switzerland
About this paper
Cite this paper
Malina, L., Clupek, V., Martinasek, Z., Hajny, J., Oguchi, K., Zeman, V. (2014). Evaluation of Software-Oriented Block Ciphers on Smartphones. In: Danger, J., Debbabi, M., Marion, JY., Garcia-Alfaro, J., Zincir Heywood, N. (eds) Foundations and Practice of Security. FPS 2013. Lecture Notes in Computer Science(), vol 8352. Springer, Cham. https://doi.org/10.1007/978-3-319-05302-8_22
Download citation
DOI: https://doi.org/10.1007/978-3-319-05302-8_22
Published:
Publisher Name: Springer, Cham
Print ISBN: 978-3-319-05301-1
Online ISBN: 978-3-319-05302-8
eBook Packages: Computer ScienceComputer Science (R0)